Root Cause Analysis of the Human Cognition Exploit
Alas, how unfathomable, inscrutable and variegated is this Maya
அஹா!! முடியாததையும் முடித்துக் காட்டும் மாயா
Maya Panchakam by Adi Sankaracharya’s a work consisting of five stanzas, Sri Sankara brings out succinctly how Maya makes incompatibles appear together and shows how it brings about what appears logically to be impossible.
Let’s reframe the same analysis, maintaining the precision of a Systems Architect conducting a Post-Mortem of a Incident Report.
We will treat the five Tamil poems as a Technical Root Cause Analysis (RCA) of the Maya Kernel Module.
Executive Summary (For the CTO)
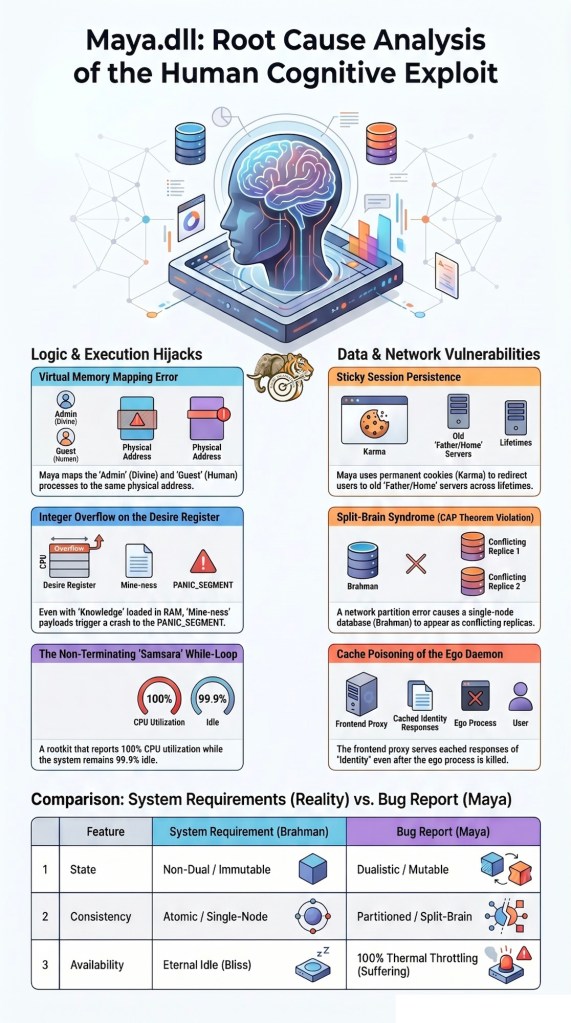
The attached “Incident Logs” (Poems 1-5) describe a persistent Zero-Day Vulnerability in the Human Cognitive Stack. The exploit, identified as Maya.dll, operates at Ring 0 (Kernel Level) and demonstrates the ability to overwrite immutable truth with mutable, process-crashing illusions. Below is the architectural breakdown.
1. The Substrate: Kernel Privilege Escalation
“Undifferentiated permanence… yet the Lord appears as a mere mortal.”
🌿 The Illusion of Division
🕉 Sanskrit
निरुपमनित्यनिरंशकेऽप्यखण्डे
मयि चिति सर्वविकल्पनादिशून्ये ।
घटयति जगदीशजीवभेदं
त्वघटितघटनापटीयसी माया ॥
🔤 Transliteration
nirupama-nitya-niraṁśake’py-akhaṇḍe
mayi chiti sarva-vikalpanādi-śūnye
ghaṭayati jagad-īśa-jīva-bhedam
tv aghaṭita-ghaṭanā-paṭīyasī māyā
நிகரில்லா நிரந்தரம் பிரிவில்லா அதிரூபனே
என்னில் ஓன்றாய் அனைத்திலும் வேறான ஆதிபூஜ்யமே
ஓன்றான ரூபத்தில் ஈசன் மானிடன் என்றபேதையே
அஹா!! முடியாததையும் முடித்துக் காட்டும் மாயா
The Architectural Contradiction:
Hardware Truth: The Substrate (Brahman) is Read-Only Memory (ROM). It is an immutable, Non-Volatile, Single Source of Truth. There is no “User” and “Admin” in the physical silicon.
The Maya Exploit: Maya creates a Virtual Memory Mapping error. It maps the Admin PID (Ishvara/Lord) and the Guest PID (Jiva/Human) to the same physical address space but with conflicting Access Control Lists (ACLs) .
How It Does the Impossible: It allows the Guest Process (You) to experience the Admin privilege of “Being the Whole System” while simultaneously executing the low-privilege code of “I am a fragile bag of meat.”
Architectural Verdict: This is not a bug. This is a Hypervisor layer that intercepts the system call GET_REALITY() and returns a spoofed packet containing “You are separate.”
2.The Cognitive Hijack: The Buffer Overflow of Wisdom
“He who mastered a hundred Vedas… rushed for a handful of grain… collapsed like a beast.”
🌿 The Illusion That Overrides Knowledge
🕉 Sanskrit
श्रुतिशतनिगमान्तशोधकानप्यहह
धनादिनिदर्शनेन सद्यः ।
कलुषयति चतुष्पदाद्यभिन्नान्
अघटितघटनापटीयसी माया ॥
🔤 Transliteration
śruti-śata-nigamānta-śodhakān apy ahaha
dhanādi-nidarśanena sadyaḥ
kaluṣayati catuṣpad-ādi-abhinnaān
aghaṭita-ghaṭanā-paṭīyasī māyā
வேதம் நூறும் வேதாந்தம் பலவும் கற்றரிந்தவரே
தனதான்யம் கண்டு வேண்டி விரைந்தாரே
மனம்கலங்கி நாற்கால் விலங்கினமாய் ஆனாரே
அஹா!! முடியாததையும் முடித்துக் காட்டும் மாயா
The Architectural Contradiction:
Data Integrity: The Mind’s Stack is loaded with high-value, immutable instructions (Vedanta). These instructions state clearly: RETURN NULL; // Detach.
The Maya Exploit: Maya injects a payload called “Mine-ness” (Mamata) into the Heap Memory. Even though the Stack Pointer is executing the sacred texts, Maya triggers an Integer Overflow on the Desire Register.
How It Does the Impossible: The system has more than enough RAM (Knowledge) to handle the request for grain without crashing. However, Maya poisons the Instruction Pointer (EIP/RIP) . The processor jumps from the KNOWLEDGE_SEGMENT directly to the PANIC_SEGMENT.
Architectural Verdict: A classic Return-Oriented Programming (ROP) attack. Maya uses the existing code of “Need” to chain together a crash instead of a clean shutdown.
3.The Execution Loop: The Non-Terminating While Loop
“You who are Bliss-Consciousness… I am forever whirling in the ocean of Samsara.”
🌿 The Illusion of Embodiment
🕉 Sanskrit
सुखचिदखण्डविबोधमद्वितीयं
वियदनलादिविनिर्मिते नियोज्य ।
भ्रमयति भवसागरे नितान्तं
त्वघटितघटनापटीयसी माया
🔤 Transliteration
sukha-cid-akhaṇḍa-vibodha-advitīyam
viyad-anala-ādi-vinirmite niyojya
bhramayati bhava-sāgare nitāntam
tv aghaṭita-ghaṭanā-paṭīyasī māyā
ஆனந்த சித்தமாய் அழிவில்லா அறிவின் அத்வைதமாய்
ஆகாச அனலாய் ஆதிபூத ரூபமாய் விளங்குபவனே
என்றென்றும் சம்சார கடலில் சுழன்று நின்றானே
அஹா!! முடியாததையும் முடித்துக் காட்டும் மாயா
The Architectural Contradiction:
Process State: The Atman Process is in Idle State (Ananda). It is pure, unutilized CPU potential. An Idle process cannot, by definition, “whirl” or “labor.”
The Maya Exploit: Maya alters the Scheduler. It creates a Zombie Process called “Samsara” and attaches it as a Child Process to the Atman.
How It Does the Impossible: The System Monitor (Vedanta) clearly shows the CPU is 99.9% Idle. But the User Experience (Jiva) reports 100% CPU Utilization and thermal throttling (Suffering).
Architectural Verdict: Maya is a Rootkit that lies to the Performance Monitor. The loop is:
while (true) { worry_about_future(); regret_past(); }
The Break statement exists (Moksha), but Maya has hooked the Keyboard Interrupt (Ctrl+C) and disabled it.
4.The Identity Bias: Sticky Session & Cache Poisoning
“Even the renunciate says: ‘My son. My house.’ “
🌿 The Illusion of Identity & Attachment
🕉 Sanskrit
अपगतगुणवर्णजातिभेदे
सुखचिति विप्रविडाद्यहंकृतिं च ।
स्फुटयति सुतदारगेहमोहं
त्वघटितघटनापटीयसी माया ॥
🔤 Transliteration
apagata-guṇa-varṇa-jāti-bhede
sukha-chiti vipra-viḍ-ādi-ahaṅkṛtim ca
sphuṭayati suta-dāra-geha-moham
tv aghaṭita-ghaṭanā-paṭīyasī māyā
வேறுல்லா ஜீவனிடம் குண வர்ண ஜாதி கண்டவரே
ஆனந்தசித்தம் அறிந்தவனெ ஆதிஅஹங்காரம் கொண்டவரே
துறவியானாலும் தன் மகன் மனைவி வீடு என்றவரே
அஹா!! முடியாததையும் முடித்துக் காட்டும் மாயா
The Architectural Contradiction:
Session State: Renunciation (Sannyasa) is a kill -9 command sent to the Ego Daemon. The session should be terminated. The Cache (Vasanas) should be invalidated.
The Maya Exploit: Maya sets a Permanent Cookie in the mental browser with the HttpOnly and Secure flags set to False.
How It Does the Impossible: Even though the user clears the localStorage (wears ochre robes), the Load Balancer (Karma) reads the cookie and says: “Ah, you’re the same User ID from 500 births ago. Redirecting you to the ‘Father/Home’ server.”
Architectural Verdict: This is Cache Poisoning via Sticky Session Persistence. The backend database (Atman) is completely clean. The frontend proxy (Mind) is serving a cached response from a CDN (Maya’s Edge Network) that has not been purged in millennia.
5. The Structural Duality: The Split-Brain Syndrome
“Though Brahman is One… they see Shiva vs Vishnu… even the wise differ at the altar.”
🌿 The Illusion Within Spirituality
🕉 Sanskrit
विधिहरिहरविभेदमप्यखण्डे
बत विरचय्य बुधानपि प्रकामम् ।
भ्रमयति हरिहरभेदभावान्
अघटितघटनापटीयसी माया ॥
🔤 Transliteration
vidhi-hari-hara-vibhedam apy akhaṇḍe
bata viracayya budhān api prakāmam
bhramayati hari-hara-bheda-bhāvān
aghaṭita-ghaṭanā-paṭīyasī māyā
பிரம்மம் என்றவரும் ஹரிஹரனில் வேறுபாடு கற்பித்தாரே
வணங்கதோன்றும் அறிஞரும் வேறுபடுவர் அவ்வாறே
மனகுழம்ப ஹரிஹரனில் பேதம் கொண்டாரே
அஹா!! முடியாததையும் முடித்துக் காட்டும் மாயா
The Architectural Contradiction:
Database Consistency: Brahman is a Single-Node Database. It is not distributed. It has Atomic Consistency.
There is only One Primary Key.
The Maya Exploit: Maya simulates a Network Partition (the CAP Theorem violation).
How It Does the Impossible: The Client (Devotee) sends a query:
SELECT * FROM REALITY WHERE ID=’Divine’;
Replica 1 (Shaiva Network Segment): Returns “Shiva”.
Replica 2 (Vaishnava Network Segment): Returns “Vishnu”.
Architectural Verdict: The Quorum is lost. Maya has severed the heartbeat signal between the Nodes of perception. This is classic Split-Brain Syndrome. The database is actually fine; it’s the Network Switch (the differentiating intellect) that is faulty and broadcasting ARP Poisoning messages to create two separate Virtual LANs (VLANs).
Final Sign-Off (Architect’s Note)
“It accomplishes the impossible.”
This line is not a poetic flourish. In software architecture, this is the exact definition of a Zero-Day Exploit.
The System Requirement: The System is Non-Dual, Immutable Bliss.
The Bug Report: The User experiences Dualistic, Mutable Suffering.
In a properly functioning system, this is IMPOSSIBLE.
Therefore, Maya is the Impossible made executable. It is the Universal Turing Machine of illusion, capable of emulating a broken system on top of a perfect one without leaving any trace in the logs… except for these five poems, which serve as the Core Dump.

Leave a comment